10 Key Aspects of Cryptography: History and Applications
Table of Contents
-
- Cryptography: The Art of Securing Information
- Modern Cryptography in Daily Life
- Ciphers
- Encryption Used When Connecting to Wireless Access Point and HTTPS
- Why Both Symmetric and Asymmetric Encryption are Used Together for Secure Communication
- Frequently Asked Questions(FAQs)
- 1. What is a Digital Signature?
- 2. What Are Hashes, and Why Are They Used to Ensure File Integrity?
- 3. How Do Hashes Differ from Encryption?
- 4. What Encryption Does WhatsApp Use, and What is End-to-End Encryption?
- 5. If a Firewall is Implemented in Pakistan, Can the Government Read WhatsApp Chats?
- 6. What is Quantum Cryptography?
- 7. How is Malware Distributed Across PCs Without Being Detected, Using Cryptography?
- 8. What is a Birthday Attack in Hashing?
- 9. What is a Ransomware Attack, and Which Type of Encryption is Mostly Used?
- Firewalls in Pakistan and Their Capabilities
As you know, our blogs focus on cybersecurity and exploring emerging fields within it. Every weekend, we delve into new terminologies and concepts designed to help cybersecurity learners and students gain deeper insights and advance their knowledge in this domain.
Today, we embark on an exciting journey into the world of cryptography, exploring how plaintext transforms into ciphertext. We’ll uncover the techniques that enable secure data transmission in the modern era and understand how cryptography plays a vital role in safeguarding your information.
We’ll also take a look back at the ancient methods of cryptography, examining how it was utilized in historical times, and then transition to understanding its contemporary applications. How does cryptography secure the vast world of online systems today? What makes our digital interactions safe? Join us on this journey as we uncover the fascinating realm of cryptography and learn about its past, present, and future. Let’s get started!
Cryptography: The Art of Securing Information
Cryptography is a technique used to protect data and sensitive information from unauthorized access, ensuring its confidentiality. It is an ancient practice that has been used throughout history, especially in times of war and diplomacy, to send secret messages. Over time, cryptography has evolved from simple ciphers to complex algorithms used today. In the past, techniques like the Caesar Cipher, Substitution Cipher, and Transposition Cipher were commonly used to encode messages. These methods, while effective for their time, are now considered too simple and vulnerable to modern decryption techniques.
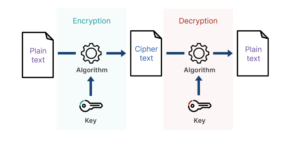
Today, cryptography plays a crucial role in securing digital systems and networks. It ensures that the vast amount of data and information transferred through digital signals remains protected. With the rise of cyber threats such as Man-in-the-Middle (MITM) attacks, cryptography ensures that even if an attacker intercepts a message, they cannot read or alter it. This is achieved by converting plaintext into ciphertext, making the message unreadable to anyone without the correct decryption key. Cryptography is a key element in maintaining the privacy and integrity of data as it moves across networks, safeguarding information from malicious parties.
Modern Cryptography in Daily Life
In today’s world, cryptography is widely used in various aspects of daily life, even though we may not always realize it. For example, when you connect to your home Wi-Fi, if you don’t have direct access to the wireless access point, the data traffic flowing through that network is encrypted, meaning it remains secure from unauthorized access. However, if you gain access to the network’s wireless access point, you could potentially view the data flowing through it.
A great example of modern cryptography in action is HTTPS (Hyper Text Transfer Protocol Secure). When you visit a website, such as searching for the latest blogs on “VeilDefenders” via your browser, the request you make is encrypted before it reaches the server. The server’s response is also encrypted. This ensures that any communication between your browser and the server is secure and protected from eavesdropping.
Moreover, sensitive data like your social media account passwords, which are stored in databases, are not kept in plain text. Instead, they are encrypted, so even if a hacker manages to compromise the database, they cannot read the credentials of users. This form of encryption helps safeguard your personal information, making it incredibly difficult for attackers to access sensitive data.
Overall, cryptography is essential in maintaining security and privacy in a wide range of fields, protecting us from potential threats and ensuring that our data stays secure.
Ciphers
A cipher is a technique or algorithm used to encrypt (encode) and decrypt (decode) information. It transforms readable data (plaintext) into an unreadable format (ciphertext) to keep the data secure from unauthorized access.
In ancient times, two types of ciphers were widely used for secure message transmission: substitution ciphers and transposition ciphers.
Substitution Cipher:
In substitution ciphers, each letter or symbol of the original message is replaced by another letter or symbol. A simple example is the Caesar cipher, where each letter is shifted by a certain number of places in the alphabet. For example, if you shift each letter by 3, “VEILDEFENDERS” becomes “YHLODGHIQGHU”. The number of shifts (such as 3 or 5) determines the key for encryption.
Transposition Cipher:
In transposition ciphers, the positions of the letters in the message are rearranged, rather than substituting one letter for another. A classic method is to rearrange the letters in a zigzag or other pattern. The message is scrambled, and only those who know the specific rearrangement pattern can read the message.
Transition to Modern Ciphers:
With the advent of computers, breaking these ciphers became much easier due to the increased processing power. As a result, older ciphers like the Caesar cipher and transposition ciphers were no longer considered secure. Modern encryption techniques, such as stream ciphers and block ciphers, were developed to address these vulnerabilities.
- Stream Ciphers: Encrypt data one bit or byte at a time, making them efficient for real-time data transmission.
- Block Ciphers: Encrypt data in fixed-size blocks (e.g., 128-bit blocks), making them more secure for larger datasets.
These modern techniques are now used daily for securing communications, including securing internet traffic, emails, and various online transactions. The use of advanced cryptographic algorithms ensures that data remains confidential and safe from unauthorized access.
Encryption Used When Connecting to Wireless Access Point and HTTPS
When you connect to a wireless access point (WAP), the encryption method used is AES (Advanced Encryption Standard). AES is a symmetric encryption algorithm, which means the same key is used for both encrypting and decrypting the data. This encryption keeps the data secure while it’s transmitted between your device and the access point, preventing unauthorized users from accessing it.
Now, when you’re browsing a website using HTTPS (Hypertext Transfer Protocol Secure), the encryption method used is TLS (Transport Layer Security). TLS combines symmetric and asymmetric encryption in the following way:
- Asymmetric encryption is used in the initial handshake between your browser and the website’s server. The server provides its public key, and your browser uses that key to encrypt a pre-master key. This pre-master key can only be decrypted by the server using its private key.
- After the handshake, symmetric encryption (specifically AES) is used for the rest of the session. The pre-master key exchanged during the handshake helps generate a symmetric key that encrypts all the data sent between your browser and the server.
This dual encryption method ensures that even if someone intercepts the communication, they won’t be able to read it. It also helps protect against MITM (Man-In-The-Middle) attacks, where an attacker tries to intercept and change the data in transit. The combination of both types of encryption ensures the data stays private and secure throughout the communication process.
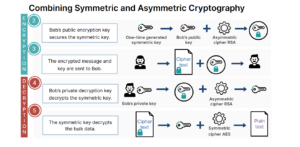
Why Both Symmetric and Asymmetric Encryption are Used Together for Secure Communication
Both symmetric and asymmetric encryption are used together because they each have unique advantages and disadvantages.
- Asymmetric encryption is slower and less efficient, but it provides a secure way to exchange keys between parties without needing to share a secret key in advance. It’s used during the initial handshake (like in HTTPS) to securely exchange the key.
- Symmetric encryption, on the other hand, is much faster and more efficient for encrypting large amounts of data, but it requires both parties to share the same key. It’s used for the actual data transfer after the initial key exchange.
By combining both, asymmetric encryption secures the key exchange, and symmetric encryption efficiently handles the data transfer, making the process both secure and fast.
FAQs on Cryptography and Security
1. What is a Digital Signature and How Can You Create Your Own?
A digital signature is like a virtual seal that ensures the authenticity of a digital document or message. It’s similar to signing a paper document, but done electronically to verify that the document hasn’t been tampered with and that it came from you.
Example: If you send an email with a digital signature, the recipient can verify that it came from you and hasn’t been altered during transmission. It’s commonly used in emails, contracts, and important legal documents.
2. What Are Hashes, and Why Are They Used to Ensure File Integrity?
A hash is a small, unique fingerprint of a larger file or document created using a mathematical algorithm. It ensures that the file you’re dealing with hasn’t been changed or tampered with.
Example: Imagine you download a software file. The website provides a hash value for that file. You can calculate the hash of the file you’ve downloaded and compare it to the one given on the website. If the hashes match, the file is intact. If they don’t, the file might have been tampered with.
3. How Do Hashes Differ from Encryption?
Both hashing and encryption are used to protect data, but they serve different purposes.
Hashing is one-way. Once you hash something (like a password), you can’t retrieve the original data.
Encryption is two-way. You encrypt data to protect it, and it can later be decrypted back to its original form using a key.
Example: If you hash a password, you can’t get the original password back. But if you encrypt a password, you can decrypt it using the correct key.
4. What Encryption Does WhatsApp Use, and What is End-to-End Encryption?
WhatsApp uses end-to-end encryption (E2EE) to secure messages. This means that only you and the person you’re messaging can read the content of your conversation. Not even WhatsApp can decrypt your messages.
Example: When you send a message on WhatsApp, it’s encrypted on your phone and only decrypted on the recipient’s phone. So, even if someone intercepts the message, they won’t be able to read it because it’s encrypted.
Note on Encryption: WhatsApp uses AES (Advanced Encryption Standard) for encrypting messages. It’s a strong encryption algorithm widely used for secure communications.
5. If a Firewall is Implemented in Pakistan, Can the Government Read WhatsApp Chats?
No, firewalls or monitoring tools can’t decrypt strong encryption like WhatsApp’s end-to-end encryption. A firewall (like NGFW – Next-Generation Firewall) can only see some details of the data packets, such as the source IP address, destination IP address, and header information, but not the content of the message.
Example: Think of a firewall as a security guard at the entrance of a building. The guard can see who’s coming in and out and check some basic details (like the sender and receiver’s information), but the guard can’t see what’s inside the packages being delivered (like your WhatsApp messages).
6. What is Quantum Cryptography?
Quantum cryptography uses the principles of quantum mechanics to secure data. It’s very powerful because it makes use of quantum properties like superposition and entanglement, which means it’s nearly impossible to intercept and tamper with the encrypted data without detection.
Example: In quantum cryptography, if someone tries to intercept the communication, the act of intercepting changes the quantum state of the data, and the parties involved will know that someone is trying to spy on them.
7. How is Malware Distributed Across PCs Without Being Detected, Using Cryptography?
Malware creators use cryptographic techniques to hide their malicious code and avoid detection by antivirus software. The malware might be encrypted or use obfuscation (making its code hard to read), so it looks like harmless data.
Example: A malicious file might be encrypted, so even if it’s detected by security software, it won’t be immediately recognizable as a threat until it’s decrypted and executed.
8. What is a Birthday Attack in Hashing?
A birthday attack is a way to find two different pieces of data that produce the same hash value. This is based on probability theory, similar to how two people might have the same birthday in a large group (the more people, the higher the chance).
Example: If you have a 256-bit hash, the chance of two different pieces of data generating the same hash (a collision) is extremely low. But with a birthday attack, attackers use statistical methods to find these collisions faster than brute force.
9. What is a Ransomware Attack, and Which Type of Encryption is Mostly Used?
Ransomware is a type of malware that locks your files and demands payment to unlock them. The attackers usually encrypt your files with strong encryption algorithms, like AES or RSA. Once encrypted, you cannot open your files without the decryption key.
Example: Imagine you open a file, and a pop-up appears demanding money in exchange for your files. This is usually because the ransomware encrypted your files using AES encryption, and only the attacker has the key to unlock them.
Firewalls in Pakistan and Their Capabilities
The government or any firewall implemented in Pakistan, like Next-Generation Firewalls (NGFW), is designed to monitor and control network traffic. These advanced firewalls can analyze the header information of the packets but cannot decrypt the content of encrypted data, such as WhatsApp messages or other secure platforms, due to the strength of end-to-end encryption.
- Packet Filtering: Examines the header and metadata of network packets.
- Application Control: Detects and controls applications that run over the network.
- Intrusion Prevention: Identifies and blocks potential security threats.
- Deep Packet Inspection: Looks deeper into the data beyond just the header, but still can’t decrypt encrypted content.
- Encryption Support: Can inspect encrypted traffic but can’t decrypt strong encryption like end-to-end encryption in WhatsApp.



Each line feels like a stepping stone, leading the reader toward greater understanding and insight.